Описание
jcvi vulnerable to Configuration Injection due to unsanitized user input
Summary
A configuration injection happens when user input is considered by the application in an unsanitized format and can reach the configuration file. A malicious user may craft a special payload that may lead to a command injection.
PoC
The vulnerable code snippet is /jcvi/apps/base.py#LL2227C1-L2228C41. Under some circumstances a user input is retrieved and stored within the fullpath variable which reaches the configuration file ~/.jcvirc.
I ripped a part of the codebase into a runnable PoC as follows. All the PoC does is call the getpath() function under some circumstances.
To run the PoC, you need to remove the config file ~/.jcvirc to emulate the first run,
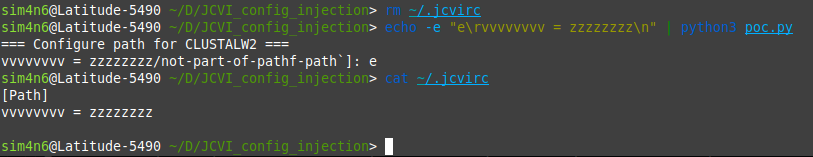
You can notice the random key/value characters vvvvvvvv = zzzzzzzz were successfully injected.
Impact
The impact of a configuration injection may vary. Under some conditions, it may lead to command injection if there is for instance shell code execution from the configuration file values.
Пакеты
jcvi
<= 1.3.5
Отсутствует
Связанные уязвимости
jcvi is a Python library to facilitate genome assembly, annotation, and comparative genomics. A configuration injection happens when user input is considered by the application in an unsanitized format and can reach the configuration file. A malicious user may craft a special payload that may lead to a command injection. The impact of a configuration injection may vary. Under some conditions, it may lead to command injection if there is for instance shell code execution from the configuration file values. This vulnerability does not currently have a fix.